I was browsing the wayback machine and thought I’d post a screenshot of our page back in December 2004. Back when we all had more time for playing around with game servers and fun 🙂
It’s been 10 years or so since I’ve posted anything meaningful to the si-ka.net network so I decided to it might be nice to start cross posting some of my technical or interesting topics from my personal blog here. Original.
I thought I’d do a quick write-up covering WiFi SSIDs on multiple VLANs, something that might be useful in a home setup, separating SSIDs better from one another. While I usually prefer the CLI, a lot of the devices mentioned here only (or mainly) use a web GUI for configuration management, so this posting will include a lot more screenshots than my usual postings. This posting won’t contain anything exciting for people who run and support networks professionally (mostly just a “so what options are available on SOHO hardware?”), and may even be overly simple and assume settings you wouldn’t do in a professional setup. But it is useful for homelab enthusiasts looking to build a more complex setup than “everything on the same VLAN/network” or trying to figure out “how do I use VLANs, give me an example”.
Ubiquiti and Netgear have some reasonable priced network gear that I’ve written about in the past that behave decent in home networks. For out little setup today we will have a WiFi access point with multiple SSIDs, two switches, and a firewall/router. We will be focusing on the configuration of the WiFi Access Point (UniFi AP) , the two Netgear switches (GS105Ev2 / GS108Ev3) and the Ubiquiti Router (Edgerouter X).
Our goal is to have two SSIDs on the access point, one for the “normal” devices (VLAN 1), and one for separate devices (VLAN 178). Since the router to VLAN 178 is on a different switch than the access point we also need to trunk both VLANs across the network. Another way of looking at it, is that we are expanding Subnet/VLAN 178 into our network (but limiting it to the WiFi Access points). 178 doesn’t hold any special meaning, you can use any VLAN number you want, just chose 178 because the subnet in this test setup was 10.0.178.0/24.
Here is a diagram of our test setup:

VLAN 1: The management and main client VLAN
VLAN 178: Subnet 178, 2nd WiFi network
Netgear 1
Port 1: Connection to Netgear 2
Port 5: Access Point
Netgear 2
Port 1: Connection to Netgear 1
Port 8: Edgerouter
Edgerouter
eth0: Connection to Subnet 178
eth1: Connection to Netgear 2
In the UniFi controller go to Settings->Wireless Networks either create a new network or edit an existing one. If you go into the advanced options area, you will find the VLAN setting for that SSID. Activating the option and setting a value means the access point will tag all packets from that SSID to the specified VLAN number.

In the network overview below we see that packets from one network are tagged with VLAN 178, and packets from the other network are untagged (the switch configuration will take care of deciding which VLAN untagged packets are part of).

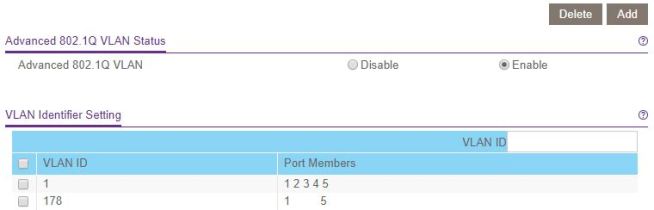
The Netgear devices only have a VLAN 1 defined by default, so the first step will be to add VLAN 178 to both of them. Enable Advanced 802.1q (VLAN->802.1Q->Advanced->VLAN Configuration), enter the VLAN ID 178 in the box and click on “Add” at the top.

Now let’s move on to the VLAN Membership configuration. To switch settings, just click on the port and it will switch from tagged->untagged->none.
Netgear 1 device
For VLAN 1 we want port 1 to be (T)agged since it is the trunk to the next switch, and all other ports (U)ntagged since they will be dealing with untagged VLAN 1 traffic. The PVID will also be set to 1 for all ports.
For VLAN 178 we want port 1 to be (T)agged since it is the trunk to the next switch, port 5 (T)agged since it is the connection to the access point, and all other ports “none” since none of those ports are part of VLAN 178.


VLAN overview after changing all the settings:
For this scenario it is sane to leave the Port PVID configuration to PVID 1 on all ports. You could change a port to 178 if you are expecting untagged traffic on that port that needs to be in VLAN 178.
Netgear 2 device
Similar configuration as the first switch so I’ll skip the screenshots. Port 1 is the connection to the Netgear 1 device, port 8 is connected to the Edgerouter.
Make sure the interface switch0 spans all ports you want to use VLANs on. Add the two VLANs 1 and 178. They should show up in the list as switch0.1 and switch0.178, and you can apply firewall rules to these interfaces to restrict traffic if you are doing any routing between the two networks.
We will want to tag everything from Subnet 178 as VLAN 178 on the interface connected to that network (eth0 in our setup), and allow VLAN 178 on the outgoing interface (eth1 in our setup). The Edgerouter doesn’t need us to specifically allow VLANs already set by the PVID, only additional VLANs need to be specified in the vid field.

You could put servers or virtual machines in their own subnet/VLAN and then use a firewall to restrict access between the different networks.
Adding more Access Points is straightforward, UniFi automatically applies the wireless configuration to all Access Points it manages, so all you need to do is take care of the switch port configuration.
Soon new laws will go into effect in the EU regarding data privacy. I assume anyone reading this has already noticed everyone updating their privacy policies. The German version of the laws exempt private websites, but the exact definition of what “private” means is a bit unclear.
To err on the side of caution we also updated our privacy policy, our impressum, and took the necessary steps behind the scenes to be complaint with the laws. The following links/forms are also in the policy itself, but for easier access:
[gdpr_preferences text=”Privacy Preferences”]
[gdpr_request_form type=”export-data”]
[gdpr_request_form type=”delete”]
Submit a request to rectify data:
[gdpr_request_form type=”rectify”]
I updated the theme today, hope this one sticks (the last one always broke evry time I did a “svn update”), also added an “Impressum” for our German readers since we use Akismet to prevent spam, and Akismet is kinda unlawful in Germany, Switzerland and Austria.
I did some comparing of server hardware today (my server is getting pretty old, must be like 4 years old by now). Anyway, I was surprised at how good a server I can get for the price I’m paying now. I’m going to have to think about it, but probably I’ll be switching from IPX over to Hetzner in the next few months. I’d have a LOT more harddisk space, AMD Athlon 64 X2 5600+, 4 GB DDR2 RAM, and 7 IPs, … the only thing I would be loosing, will be the possibility to to a hard reset.
Ich habe mal wieder einen HackIt Server aufgeseztzt. Das bedeutet ich stelle einen Server ins Internet, und ihr dürft (sollt) versuchen ihn zu “hacken”. Zu gewinnen gibt es nichts (abgesehen davon den Wissenshorizont zu erweitern). Nun zu die Details:
IP: 80.190.250.213
Auf die Kiste läuft ein Webserver http://80.190.250.213/ mit eine knappe Beschreibung vom Wettbewerb, Ziele und Regeln. Der Webserver ist diesesmal das Ziel vom Wettbewerb, es geht darum die diese Seite zu “entstellen” (also ein Defacement). Um das ganze ein wenig interessanter zu gestalten werden alle ssh sessions mit “script” aufgezeichnet und, für jeden zugänglich, hier gespeichert (die Dateien kann man z.B. mit “less -r datei” anschauen).
Regel und Ziel des Wettbewerbs:
Wie oben schon erwähnt geht es darum diese Seite zu entstellen. Generell ist dazu alles erlaubt, ich möchte euch so wenig wie möglich einschränken, seid kreativ und einfallsreich.
Dennoch muss ich eine kleine Liste an Aktionen aufstellen die nicht erlaubt sind.
A few details to the box and the system:
So, und nun habt Spaß damit 😉
Ich werde zwar Aktualisierungen auch hier posten, ich denke aber, dass die meisten Infos (auch von Teilnehmer) vorwiegend auf der buha Seite und in meinen Blog ausgetauscht werden.
Na Jungs, ich suche Ideen was wir mit si-ka.net anfangen könnten. Was sagt eure Kreativität? Alle Paar monate mal ein neues browserspiel ausprobieren? Mal ein richtiges opensource spiel von freshmeat oder sourceforge schnappen mit echte grafik?
momentan dümpelt die seite so vor sich hin 😉
Eigentlich hatte ich vor, einfach die Passwort Hashes vom alten Forum zu nehmen und hier direkt in den Datenbank ‘reinzuschieben. Beide machen MD5, einer von beiden macht noch irgendwas komisches zusätzlich, auf jeden fall passen die phpBB hashes nicht wenn ich die hier benutzen will, d.h. ich lege eure User mit Defaultpasswörter an die ihr ändern könnt nach den einloggen.
… und weil ich grad so schön am tippen bin, wer sich neu Registriert sollte mir eine kleine Infos zukommen lassen, damit ich denjenigen schreibrechte hier geben kann 😉
Da Blizz uns gerade das leben etwas schwer macht, trotz legal gekaufter Starcraft, im Battlenet zu spielen. Habe ich mich ein wenig umgeschaut, was es für alternativen gäbe. Da gibt es doch tatsächlich ein Opensource Battlenet Server … der mit etwas Geschick auch zu laufen scheint. Damit der im Client auftaucht braucht man eine kleinen Registry Änderung:sika-battlenet Wer interesse hat kann auch den Editor sich anschauen und selber damit herumspielen (auch nütlich um die Defaultwerte wiederherzustellen) bneteditor
Jaja, ich weiß, schon wieder eine neue Webseite … Das Forum war einfach unpraktisch für unsere Zwecke, dafür posten wir einfach zu selten etwas. So ist es wesentlich einfacher den Überblick zu behalten.